A widespread use case for enterprise customers is to host applications in the cloud and provide secure access to those applications from any part of the world. Using Alkira CXP secure access to applications from any part of the world is seamless and configuration is simple, fast, and secure. Users can configure even complex traffic policy with just a few clicks. In fact, there are only two steps to managing ingress traffic with Alkira. Let’s take a look at how it all works.
CSP Native Approach
In traditional Cloud Service Provider (CSP) approach for ingress traffic, the packet will hit the load balancer first, with the firewall as a target to inspect traffic. The SNAT and DNAT rules need to be configured on the firewalls so that traffic can hit the destination, which is the end application sitting in the VPC/VNET/VCN, and the return traffic comes back to the same firewall for traffic symmetry.
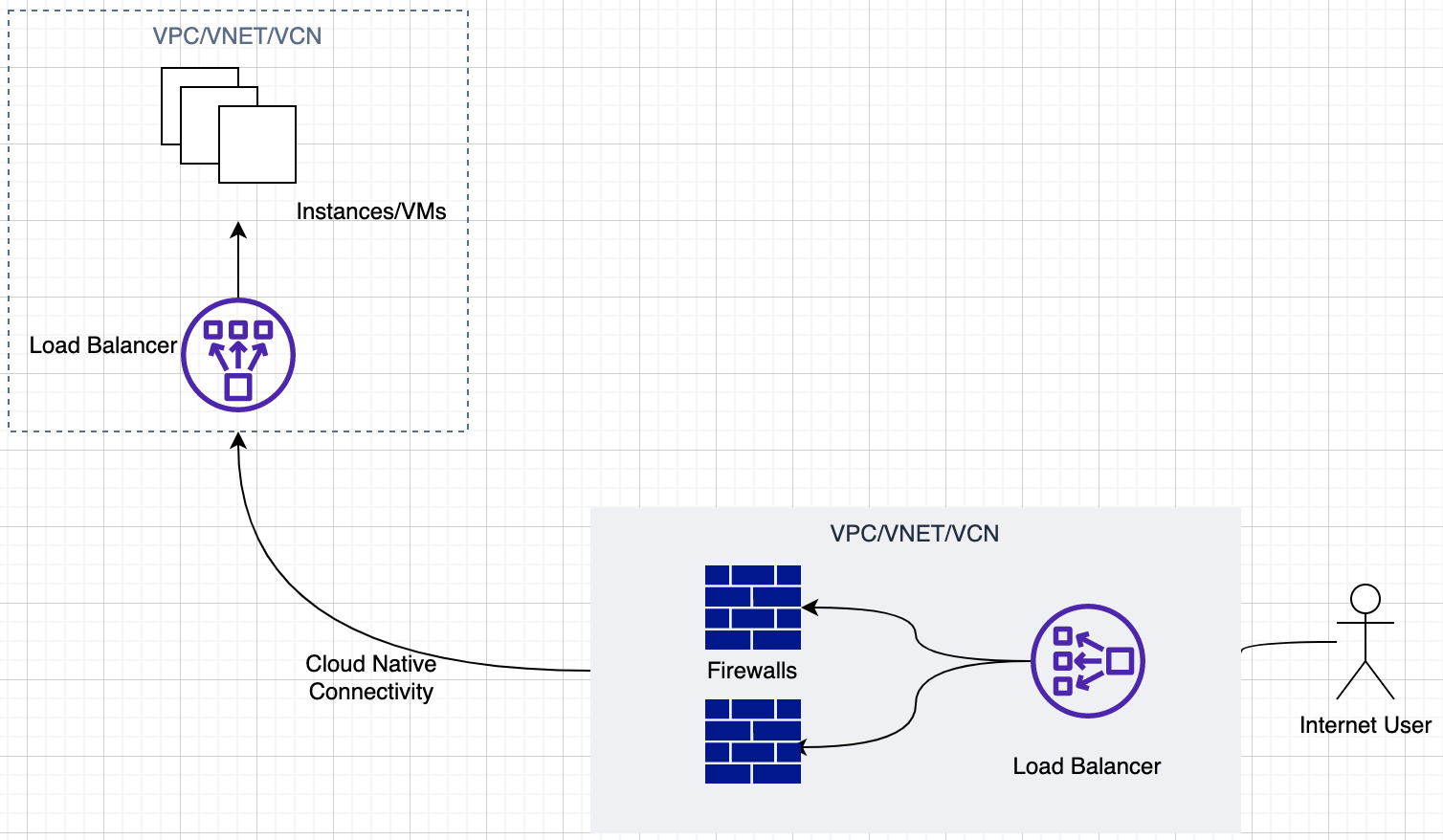
Figure 1: The traditional model for ingress traffic management
Challenges with this Approach:
Routing Complexity
Every CSP has different constructs like a routing table, a subnet, an internet gateway, UDR, VNG, etc., which work in different ways. When applications are deployed in a Multi-Cloud environment, managing and operating these constructs becomes even more complex, and it becomes a challenge to have an optimal design.
Partial Visibility
When deploying the application in the CSP environment natively, the SNAT and DNAT rules are required for establishing communication. The problem with this approach is that Client IP preservation is not possible; hence network operators won’t have end-to-end traffic visibility.
Maintaining Traffic flow Redundancy
In the case of a redundant firewall deployment, maintaining traffic flows for an active-active scenario will be challenging because load balancing between the firewall is not possible when SNAT and DNAT rules are configured.
Configuration Complexity
NAT requirement in the native approach will add the configuration complexity in the environment and make it operationally hard to manage the network.
The Alkira Approach for Ingress Traffic Management
Alkira can do the above use case of ingress traffic protection seamlessly once the user has applied the relevant configuration on the Alkira CXP. The Ingress traffic from the Internet will hit the CXP; traffic will be redirected to the firewall instances; once the traffic has been inspected, the traffic will be sent to the end application.
The ingress policy on Alkira CXP gives flexibility to the user to steer the traffic depending on the use case.
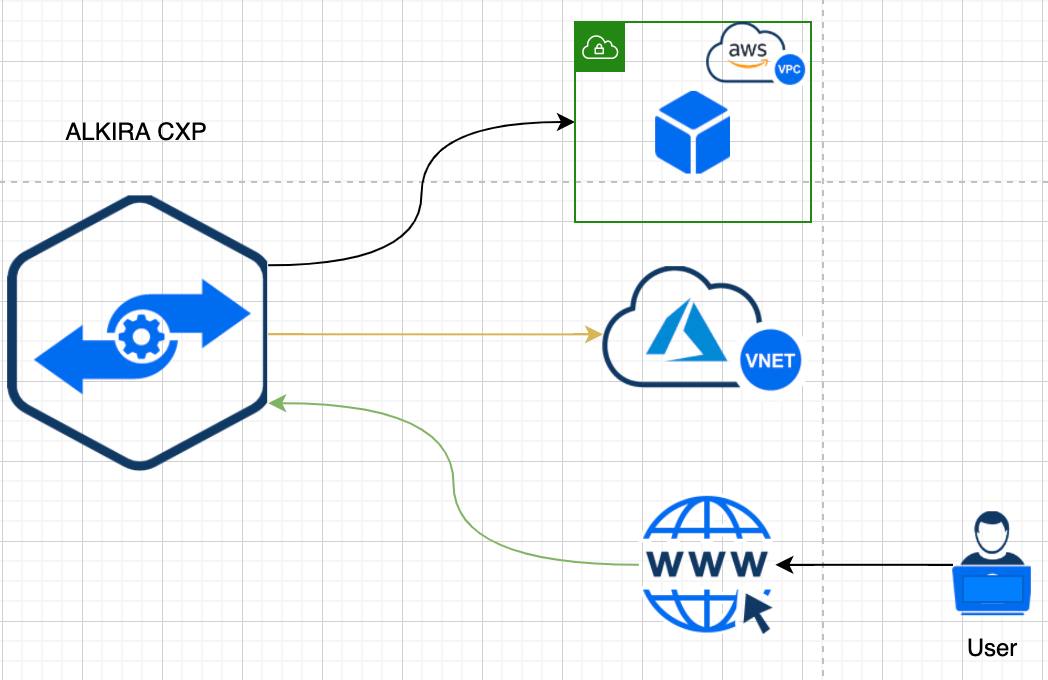
Figure 2: Alkira CXPs make managing and steering traffic simple and easy
The configuration has just two steps:
1- Define the Application
2- Create a Traffic Policy to steer traffic toward the application
3- That’s it – There is no step three!
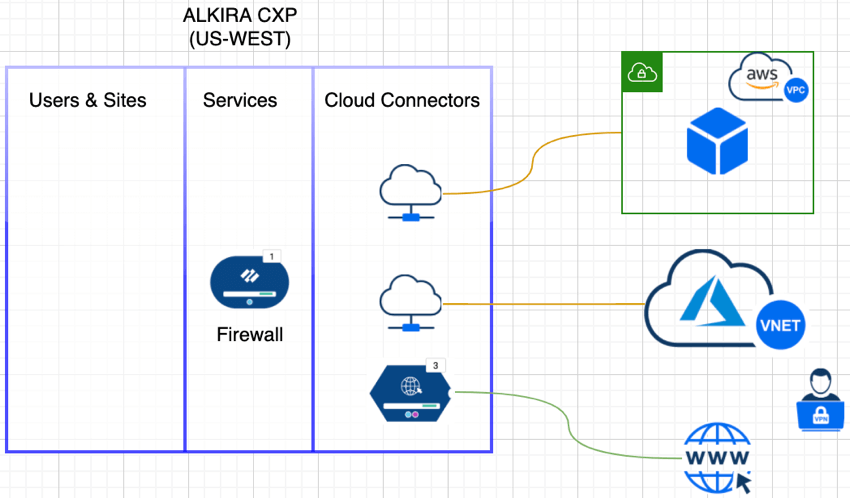
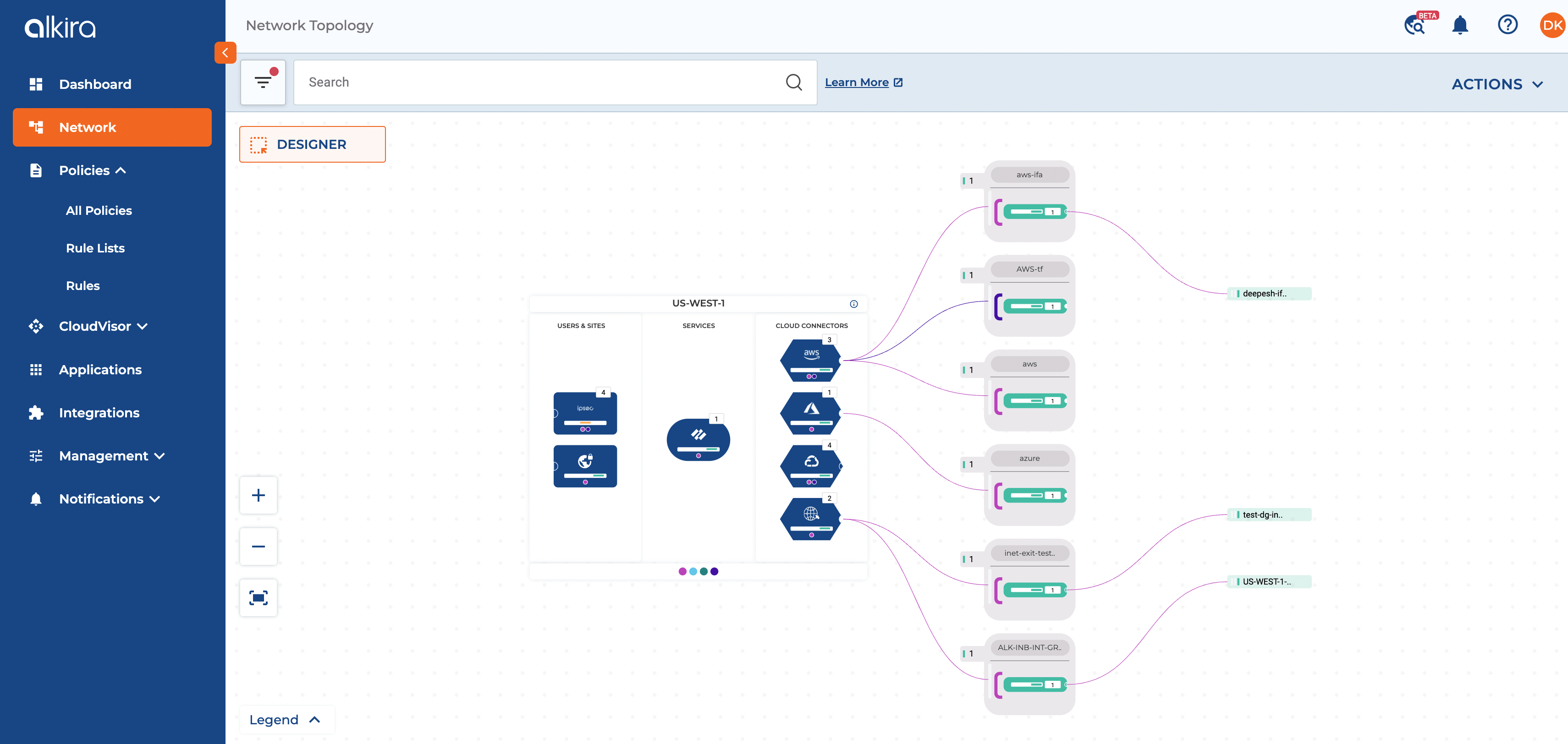
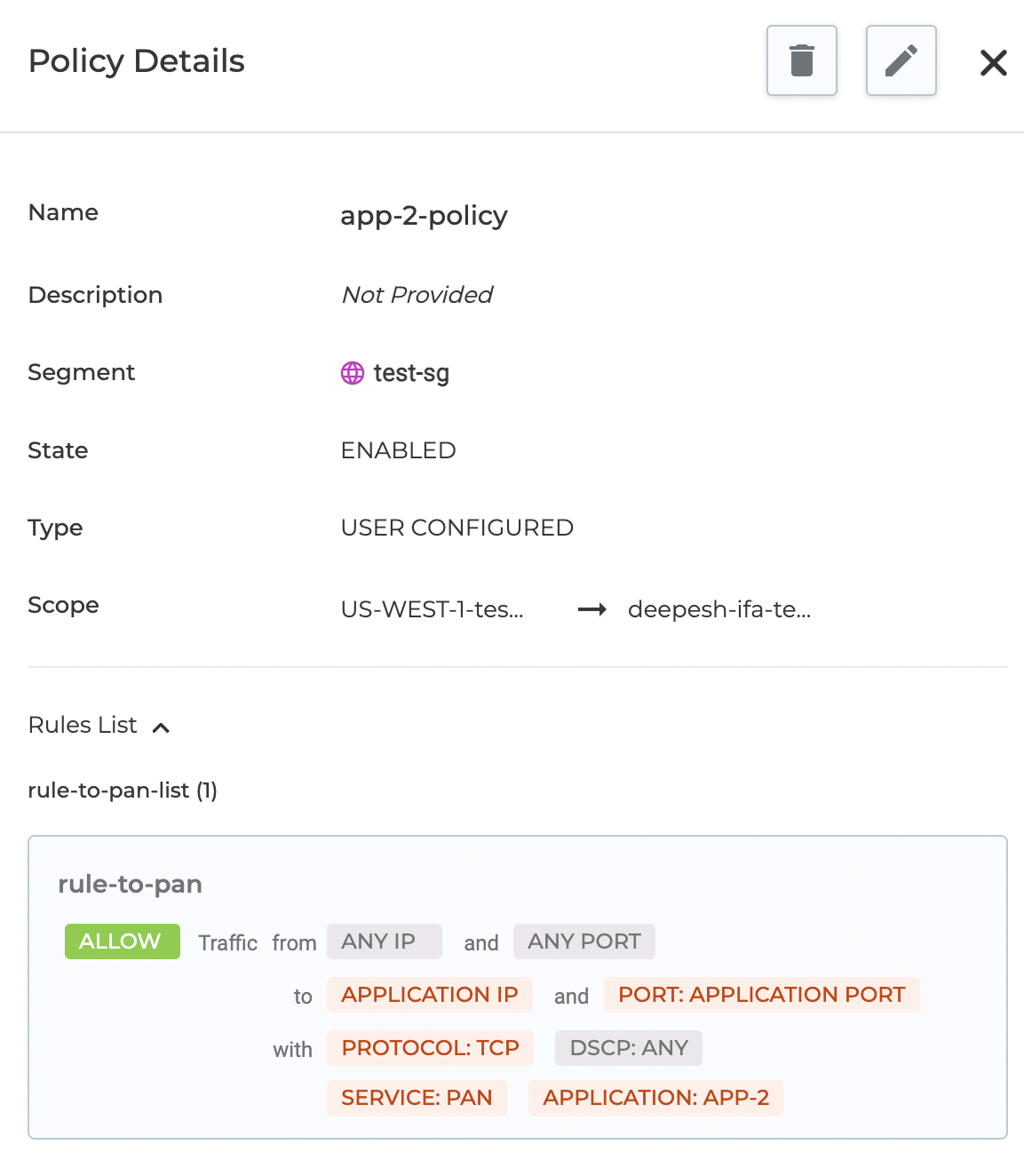
Figure 3-5:The Alkira platform delivers simple and powerful traffic management, with end-to-end visibility and seamless multi-cloud capabilities
Alkira Solution Benefits:
Secure Multi-Cloud Approach
Alkira solution is built with simplifying cloud networking in mind and gives the customer a cloud-agnostic experience, and eliminates the need of configuring each CSP construct individually without compromising security.
End-to-End Visibility
Since no NAT configurations are required, client IP preservation will automatically be handled when traffic is sent through Alkira CXP.
Redundancy
In the case of Active-Active firewall deployment, maintaining traffic flow symmetry is easier since no NAT rules are configured, and load balancing is achieved using different hashing algorithms.
Ease of Configuration
Configuration of Ingress traffic is straightforward, wherein the user needs to configure the traffic policy and the relevant application information.
Modernize your cloud network with Alkira
To learn more about how Alkira can help simplify cloud networking for your organization, reach out and schedule a demo today.
You can also try our Cloud Insights tool for free here, giving you instant inventory and insights into your cloud networking resources.
Ahmed Abeer is a Sr. Product Manager at Alkira, where he is responsible for building a best-in-class Multi-Cloud Networking and Security Product. He has been in Product Management for more than ten years in different big and small organizations. He has worked with large enterprise and service provider customers to enable LTE/5G MPLS network infrastructure, automate Layer 3 Data Center, enable Next-Gen Multi-Cloud architecture, and define customers’ Multi-Cloud strategies. Ahmed’s technical expertise in Cloud Computing and Layer 2/Layer 3 network technologies. Ahmed is a public speaker at various conferences & forums and holds a Master’s Degree in Computer Engineering
Deepesh Kumar is a Solutions Architect and product specialist in the computer networking industry with over 8 years of experience. He currently works as part of the post sales team at Alkira and focuses on working with customers to design and deploy the Alkira solution. Prior to working here, he worked at Viptela which was acquired by Cisco Systems. He holds a masters degree from San Jose State University.