Frequently Asked Questions
Deployment & Integration
How does Alkira simplify the deployment of Palo Alto Networks VM-Series Firewalls in AWS compared to manual methods?
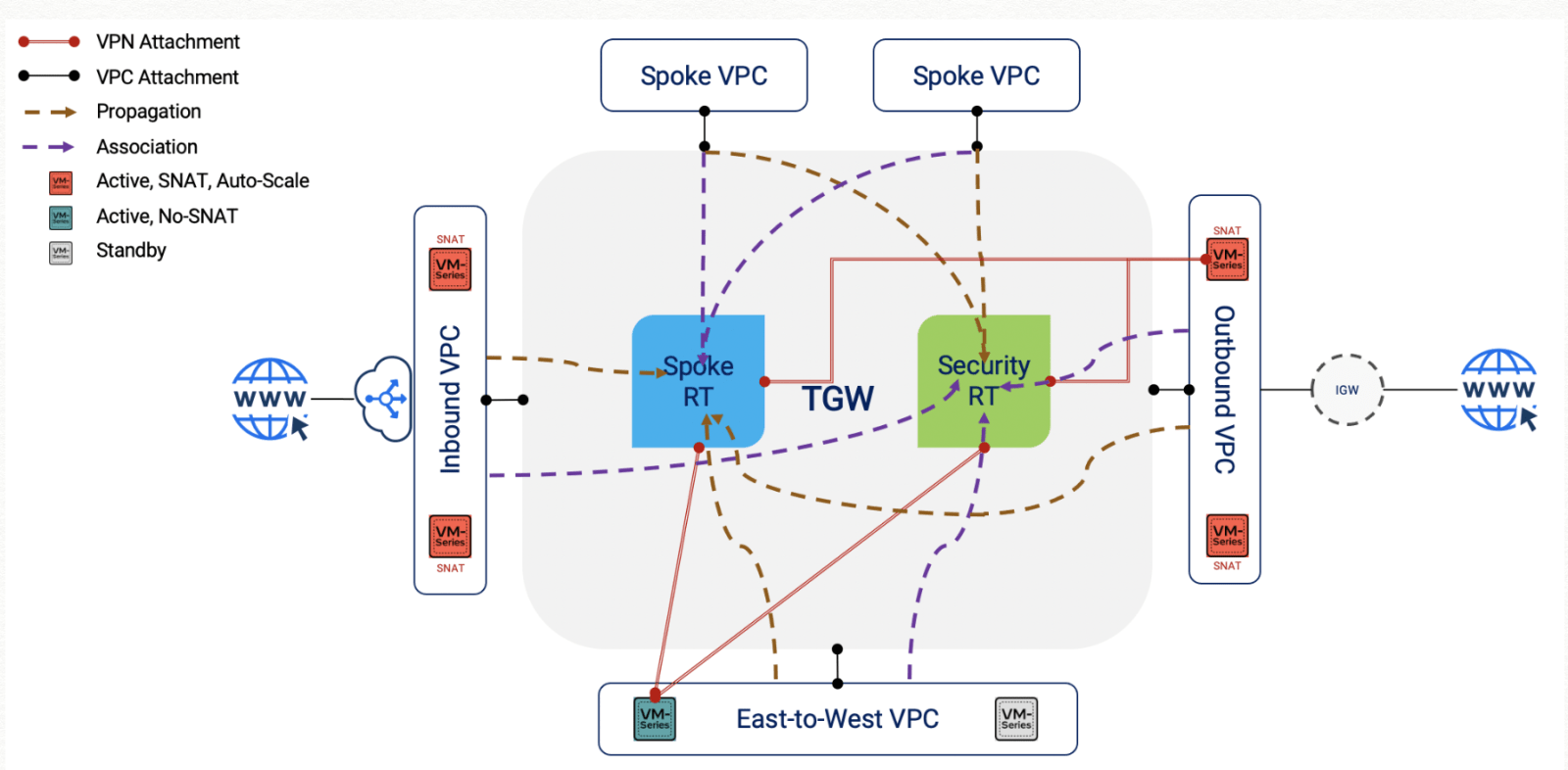
Alkira enables a streamlined, three-step deployment process for Palo Alto Networks VM-Series Firewalls in AWS. Instead of manually configuring multiple VPCs, route tables, and attachments, you can provision firewalls directly inside Alkira Cloud Exchange Points (CXPs) from the topology canvas. This eliminates the need for deep AWS networking expertise and reduces deployment complexity, making it simple and standardized across regions and cloud providers. [Source]
What are the three steps to deploy Palo Alto Networks VM-Series Firewalls with Alkira?
The three steps are: 1) Deploy Palo Alto VM-Series Firewalls inside Alkira Cloud Exchange Points (CXPs), 2) Map segments/groups to the firewall zones, and 3) Define Alkira policy to steer traffic to the firewalls. This process is managed through Alkira's Cloud Area Networking portal, providing speed, simplicity, and elasticity. [Source]
Can Alkira support both BYOL and PAYG licensing models for Palo Alto Networks VM-Series Firewalls?
Yes, Alkira supports both Bring Your Own License (BYOL) and Pay As You Go (PAYG) models for Palo Alto Networks VM-Series Firewalls. You only need to provide the license information during provisioning. [Source]
How does Alkira handle segmentation and micro-segmentation for firewall deployments?
Alkira allows administrators to assign segments and groups to connectors during onboarding. Segments are isolated compartments for routing and policy, while groups enable micro-segmentation. These can be mapped directly to Palo Alto Networks VM-Series Firewall zones, providing granular and flexible security policies without manual configuration. [Source]
What is the role of Alkira Cloud Exchange Points (CXPs) in firewall deployment?
Alkira CXPs are the core infrastructure elements where Palo Alto Networks VM-Series Firewalls are provisioned. They enable seamless integration, autoscaling, and lifecycle management of firewalls, supporting both cloud and on-premise connectors. [Source]
How does Alkira's autoscale feature work with Palo Alto Networks VM-Series Firewalls?
Alkira's autoscale feature monitors traffic through the firewalls and automatically scales the number of firewall instances up or down based on load. This optimizes resource utilization and ensures you only pay for what you need. [Source]
Can Alkira integrate with Palo Alto Networks Panorama for firewall management?
Yes, Alkira supports integration with Palo Alto Networks Panorama. Enterprises can manage firewalls provisioned within Alkira CXPs through Panorama by providing the Panorama server IP, device group, and template information. [Source]
How does Alkira's policy framework steer traffic to Palo Alto Networks VM-Series Firewalls?
Alkira uses an intent-based, point-and-click policy framework to steer traffic to the VM-Series firewalls. Administrators can define policies based on 5-tuple matches within segments, choosing to permit and send traffic to the firewall, permit without sending, or deny and drop traffic. [Source]
Is it possible to expand firewall deployments to multiple clouds and regions with Alkira?
Yes, Alkira makes it easy to expand firewall deployments to additional clouds and regions. You can add more Alkira CXPs with VM-Series firewalls or add cloud connectors for new clouds, and map them to the appropriate groups and firewall zones. [Source]
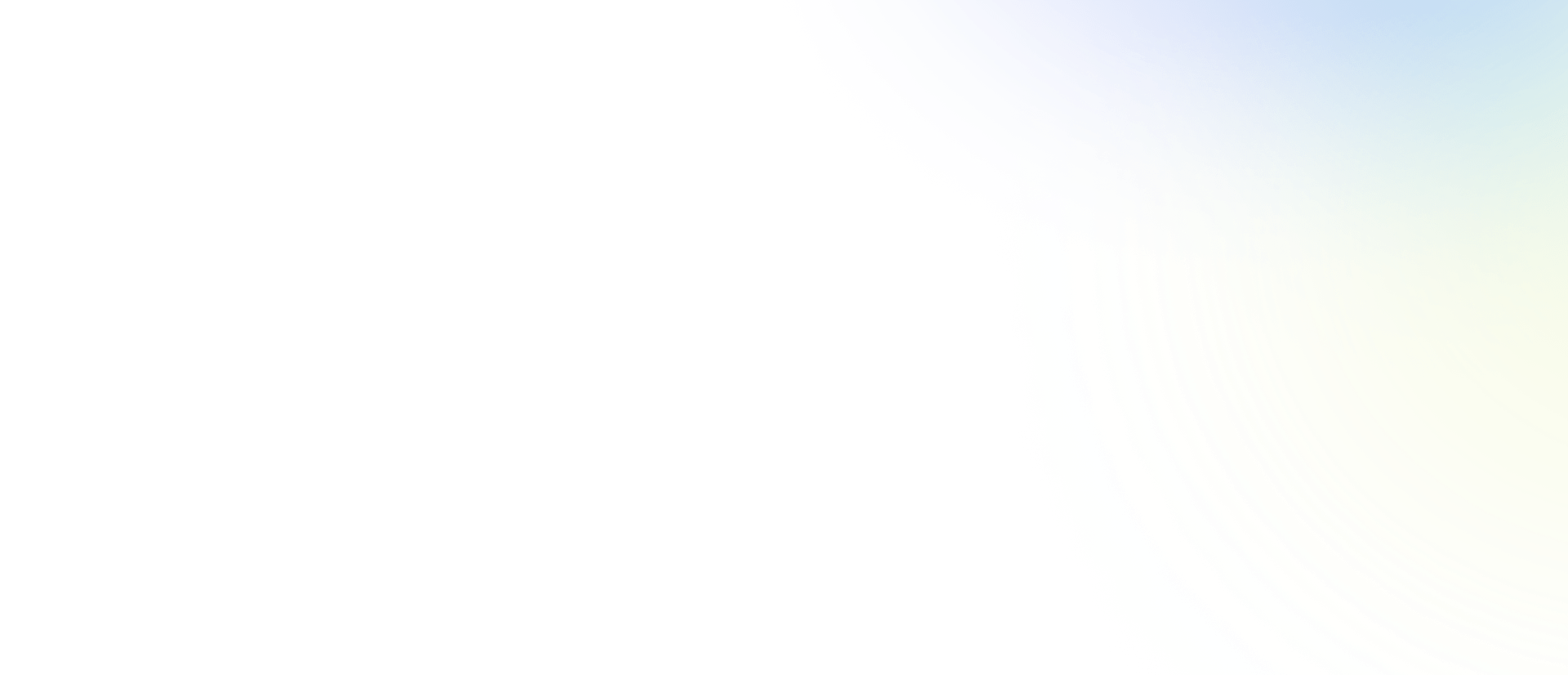
What challenges do enterprises face when deploying Palo Alto Networks VM-Series Firewalls manually in AWS?
Manual deployment requires deep knowledge of AWS networking constructs, including VPCs, route tables, TGW attachments, and route propagation. It becomes even more complex with multiple segments, security zones, or regions, and maintaining traffic symmetry is challenging. Alkira eliminates these complexities with automation and abstraction. [Source]
How does Alkira help maintain traffic symmetry and optimal firewall utilization?
Alkira's autoscale and policy-based traffic steering ensure that traffic is distributed efficiently across firewall instances, maintaining symmetry and optimizing resource utilization, even across multiple regions and clouds. [Source]
What are the benefits of using Alkira for Palo Alto Networks VM-Series Firewall deployments?
Benefits include simplified deployment, reduced operational complexity, support for autoscaling, seamless integration with Panorama, granular segmentation, and the ability to expand across clouds and regions with minimal effort. [Source]
How does Alkira's solution compare to cloud-native deployment models for firewalls?
Alkira abstracts away the complexity of cloud-native networking constructs, automates segmentation and policy mapping, and provides a unified interface for deployment and management, making it more scalable and easier to operationalize than cloud-native models. [Source]
Can Alkira's solution be used for both cloud and on-premise environments?
Yes, Alkira supports both cloud and on-premise connectors, allowing you to extend segmentation and security policies seamlessly across hybrid environments. [Source]
How does Alkira manage the lifecycle of Palo Alto Networks VM-Series Firewall VMs?
Alkira manages the full lifecycle of firewall VMs, including provisioning, scaling, and decommissioning, while enterprises can use Panorama for ongoing management and policy configuration. [Source]
What is required to provision a Palo Alto Networks VM-Series Firewall in Alkira?
To provision a VM-Series Firewall in Alkira, you need the license information (BYOL or PAYG). If using Panorama, you also need the Panorama server IP, device group, and template details. [Source]
How does Alkira support policy-based traffic steering for different use cases?
Alkira's intent-based policy framework allows you to define granular traffic steering rules based on segments, groups, and 5-tuple matches, supporting a wide range of use cases such as internet access, east-west traffic, and hybrid connectivity. [Source]
What is the advantage of using Alkira for multi-region and multi-cloud firewall deployments?
Alkira provides a unified, automated approach to deploying and managing firewalls across multiple regions and clouds, reducing operational overhead and ensuring consistent security policies everywhere. [Source]
How does Alkira's solution impact speed and agility for IT teams?
Alkira enables IT teams to deploy enterprise-grade security firewalls in the cloud quickly and efficiently, without compromising on functionality or requiring deep cloud networking expertise. This leads to faster time-to-value and greater business agility. [Source]
Features & Capabilities
What integrations does Alkira offer for security and automation?
Alkira integrates with leading security solutions such as Palo Alto Networks, Cisco, Fortinet, and Check Point for next-generation firewalls and Zero Trust Network Access (ZTNA). It also integrates with Splunk for observability, Terraform for automation, and Infoblox for DNS/IP management. [Source]
Does Alkira provide an API for integration and automation?
Yes, Alkira provides an API for developers and users to integrate platform functionalities into their systems. Detailed documentation and resources are available on Alkira's API documentation page. [Source]
What technical documentation is available for Alkira's platform?
Alkira offers whitepapers, solution briefs, and a dedicated wiki for in-depth technical information. These resources cover use cases, partnerships, and detailed platform capabilities. [Source]
What security and compliance certifications does Alkira hold?
Alkira is SOC 2 and PCI-DSS compliant, ensuring high standards for security, availability, confidentiality, and protection of cardholder data. These certifications are independently verified and reflect Alkira's commitment to secure cloud networking. [Source]
What are the key features of Alkira's platform for firewall deployments?
Key features include drag-and-drop deployment, autoscaling, vendor-agnostic integration, granular segmentation, intent-based policy, and support for both cloud and on-premise environments. [Source]
How does Alkira support Zero Trust Network Access (ZTNA)?
Alkira integrates ZTNA as a core feature, ensuring secure access for distributed workforces and applications, and supporting next-generation firewall deployments for comprehensive security. [Source]
What is Alkira's approach to vendor lock-in?
Alkira takes a vendor-agnostic approach, allowing customers to choose their preferred security and network stack components, including Palo Alto Networks, without being locked into a single vendor. [Source]
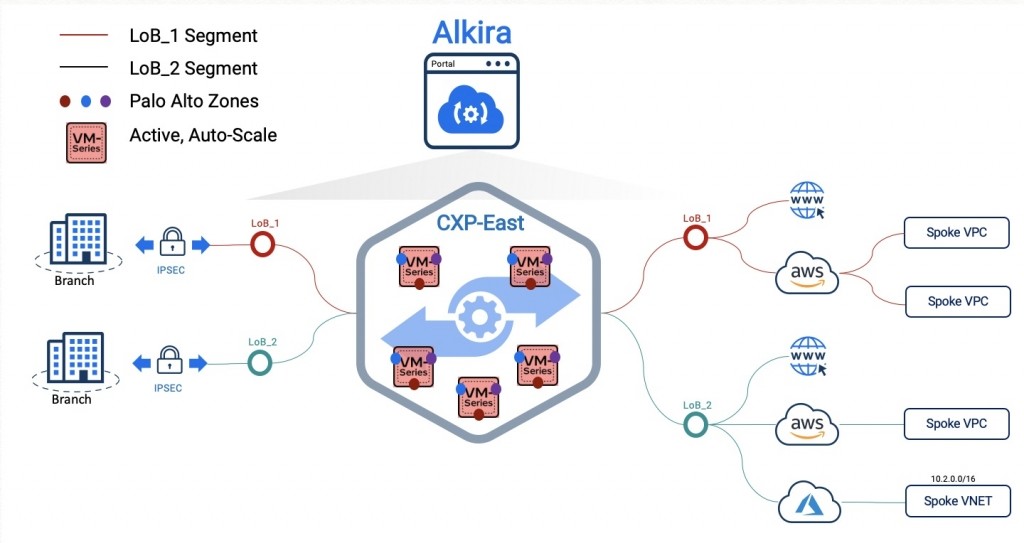
How does Alkira provide visibility and governance for firewall deployments?
Alkira offers single-pane-of-glass tools for monitoring and managing cloud networks, ensuring comprehensive visibility, governance, and control over firewall deployments and network traffic. [Source]
What is the typical implementation timeline for Alkira's platform?
Customers can implement a proof of concept in as little as 4 hours, with full production deployments typically completed in about 8 weeks. This rapid deployment minimizes disruption and accelerates time-to-value. [Source]
How does Alkira's drag-and-drop interface benefit users?
Alkira's drag-and-drop interface simplifies network design and deployment, making it accessible even for non-technical users and reducing the need for extensive technical resources. [Source]
What customer feedback has Alkira received regarding ease of use?
Customers have praised Alkira for its intuitive drag-and-drop interface, rapid deployment (POC in 4 hours), and minimal resource requirements. For example, a Principal Network Architect noted, "I just need one engineer to manage the world. Otherwise, 10 engineers." [Source]
What is Alkira's pricing model?
Alkira offers both consumption-based (pay-as-you-go) and commitment-based pricing models. Pricing is tailored to each customer based on network elements, connectors, firewalls, and bandwidth. Fixed hourly rates are available for specific components. [Source]
How can I get a personalized quote for Alkira's services?
You can request a personalized quote by completing a form on Alkira's pricing page. Alkira will provide a custom proposal based on your specific requirements. [Source]
Use Cases & Benefits
What business impact can customers expect from using Alkira's platform?
Customers can expect up to 96% reduction in cloud setup time, 47% reduction in network management time, up to 40% lower TCO, and improved service quality with a 70% reduction in mean-time-to-resolution for complex issues. [Source]
What pain points does Alkira solve for enterprises deploying firewalls in the cloud?
Alkira addresses pain points such as complex intra-cloud connectivity, global traffic inefficiencies, design sprawl, inconsistent performance, high costs, operational complexity, and lack of visibility and governance. [Source]
Who can benefit from Alkira's solution for firewall deployments?
Alkira's solution benefits technical roles (network, cloud, security architects, IT managers), business leaders (VP, CTO, CIO, CISO), and organizations operating in multicloud or hybrid environments seeking to simplify networking and enhance security. [Source]
What industries have successfully used Alkira's platform?
Industries include manufacturing, retail, healthcare, financial services, media & entertainment, telecommunications, biotech, software, and aviation. [Source]
Can you share customer success stories related to firewall deployments?
Yes, for example, Michaels transformed its network across 1,400 stores in record time, and Koch Industries reduced network complexity and improved agility. More case studies are available on Alkira's Customers Page. [Source]
How does Alkira help enterprises achieve measurable ROI?
Alkira reduces cloud setup time by 96%, network management time by 47%, and delivers up to 40% lower TCO compared to traditional solutions, resulting in significant operational cost savings. [Source]
What is Alkira's vision and mission?
Alkira's vision is to simplify and enhance networking across multicloud and hybrid cloud environments, transforming enterprise connectivity through Network Infrastructure-as-a-Service (NIaaS). [Source]
What makes Alkira different from other cloud networking solutions?
Alkira offers a true abstraction layer, vendor-agnostic integration, drag-and-drop interface, global backbone-as-a-service, integrated security, and measurable ROI, making it easier and faster to deploy and manage firewalls across clouds. [Source]
How does Alkira compare to competitors for firewall deployments?
Alkira stands out with its vendor-agnostic approach, ease of use, rapid deployment (POC in 4 hours), integrated security, and comprehensive visibility, offering flexibility and operational efficiency not typically found in traditional or cloud-native solutions. [Source]
What support and training resources does Alkira provide?
Alkira provides comprehensive training resources, including detailed guidance, demos, whitepapers, solution briefs, and a dedicated wiki to help customers efficiently learn and implement the solution. [Source]
How can I request a demo of Alkira's platform?
You can schedule a demo directly through Alkira's website to see the platform in action and discuss your specific requirements with their team. [Source]